Boosted by baldur@toot.cafe ("Baldur Bjarnason"):
dingemansemark@scholar.social ("Mark Dingemanse") wrote:
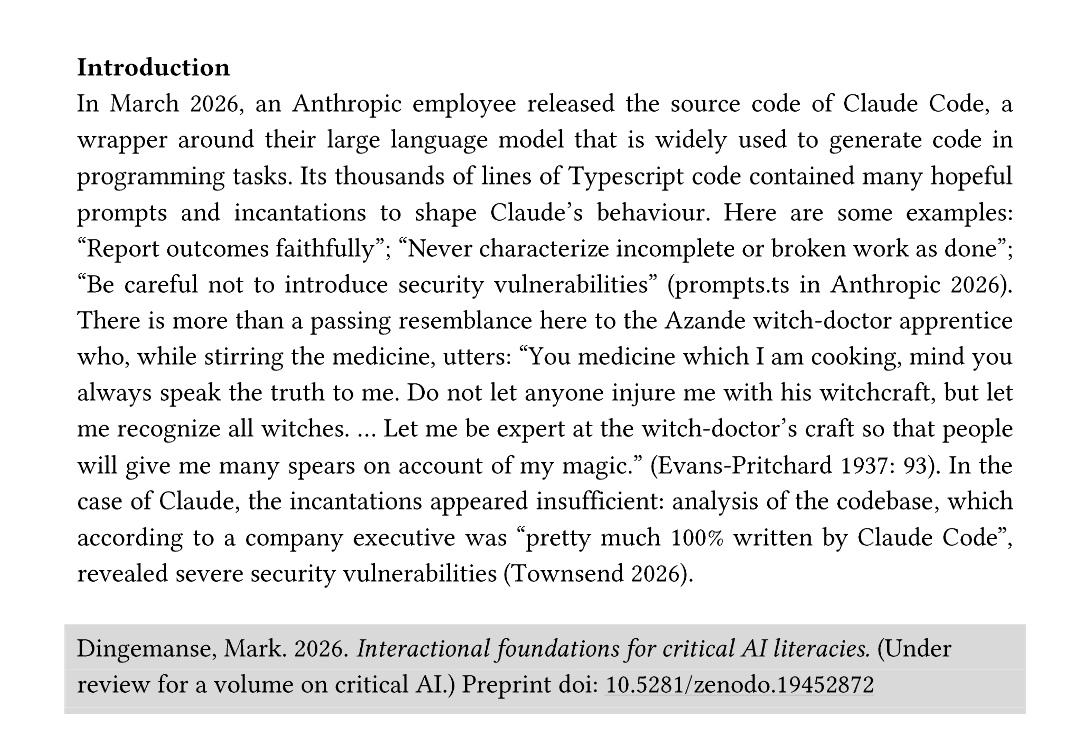
I was supposed to finish this last week but then the #Claude Code leak happened, promptly giving me an excellent opening example (h/t @jonny for their digital archaeology work that drew my attention to the magic prompting techniques)
(I think it is likely btw that #Anthropic shifted the #Mythos announce forward to this week to bury the leak & its security implications)