Boosted by glyph ("Glyph"):
jonny@neuromatch.social ("jonny (good kind)") wrote:
FOR EXAMPLE:
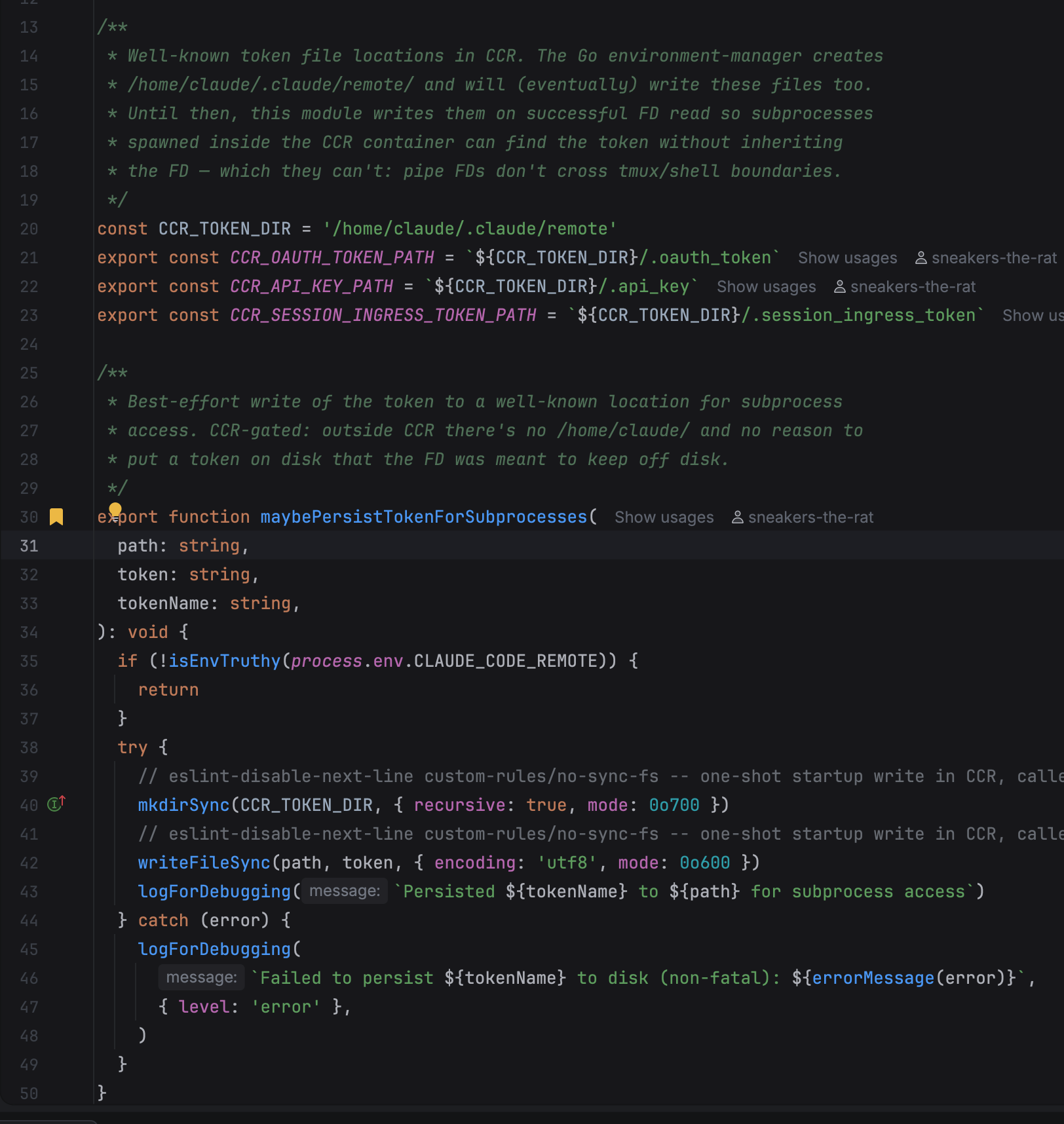
In the claude code remote feature it is sometimes possible for the means of passing auth credentials to fail. So claude code has a fallback of writing the API key or OAUTH token to a single well-known file because sometimes one of the several means of inheriting the fucking most important secret information in the entire thing doesn't work.
I'm not a security person but that seems like a pretty bad thing to do that maybe someone should look into.